A brand new malware botnet was once came upon focused on Realtek SDK, Huawei routers, and Hadoop YARN servers to recruit units into DDoS (allotted denial of carrier) swarm with the potential of huge assaults.
The brand new botnet was once came upon through researchers at Akamai originally of the yr, who stuck it on their HTTP and SSH honeypots, observed exploiting previous flaws comparable to CVE-2014-8361 and CVE-2017-17215.
Akamai feedback that HinataBotâs operators to start with allotted Mirai binaries, whilst HinataBot first gave the impression in mid-January 2023. It sort of feels to be in accordance with Mirai and is a Pass-based variant of the infamous pressure.
After taking pictures more than one samples from lively campaigns as not too long ago as March 2023, Akamaiâs researchers deduced that the malware is underneath lively construction, that includes practical enhancements and anti-analysis additions.
Vital DDoS energy
The malware is shipped through brute-forcing SSH endpoints or the usage of an infection scripts and RCE payloads for recognized vulnerabilities.
After infecting units, the malware will quietly run, looking forward to instructions to execute from the command and regulate server.
Akamai’s analysts created a C2 of their very own and interacted with simulated infections to degree HinataBot for DDoS assaults to look at the malware in motion and infer its assault functions.
Older variations of HinataBot supported HTTP, UDP, ICMP, and TCP floods, however the more moderen variants best function the primary two. On the other hand, even with best two assault modes, the botnet can probably carry out very robust allotted denial of carrier assaults.
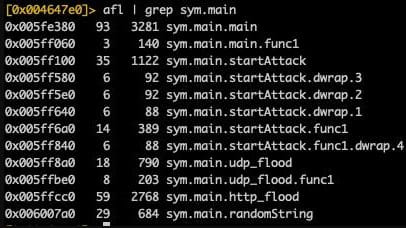
Whilst the HTTP and UDP assault instructions range, they each create a employee pool of 512 staff (processes) that ship hardcoded information packets to the objectives for an outlined length.
The HTTP packet measurement levels between 484 and 589 bytes. The UDP packets generated through HinataBot are in particular huge (65,549 bytes) and encompass null bytes able to overwhelming the objective with a big site visitors quantity.
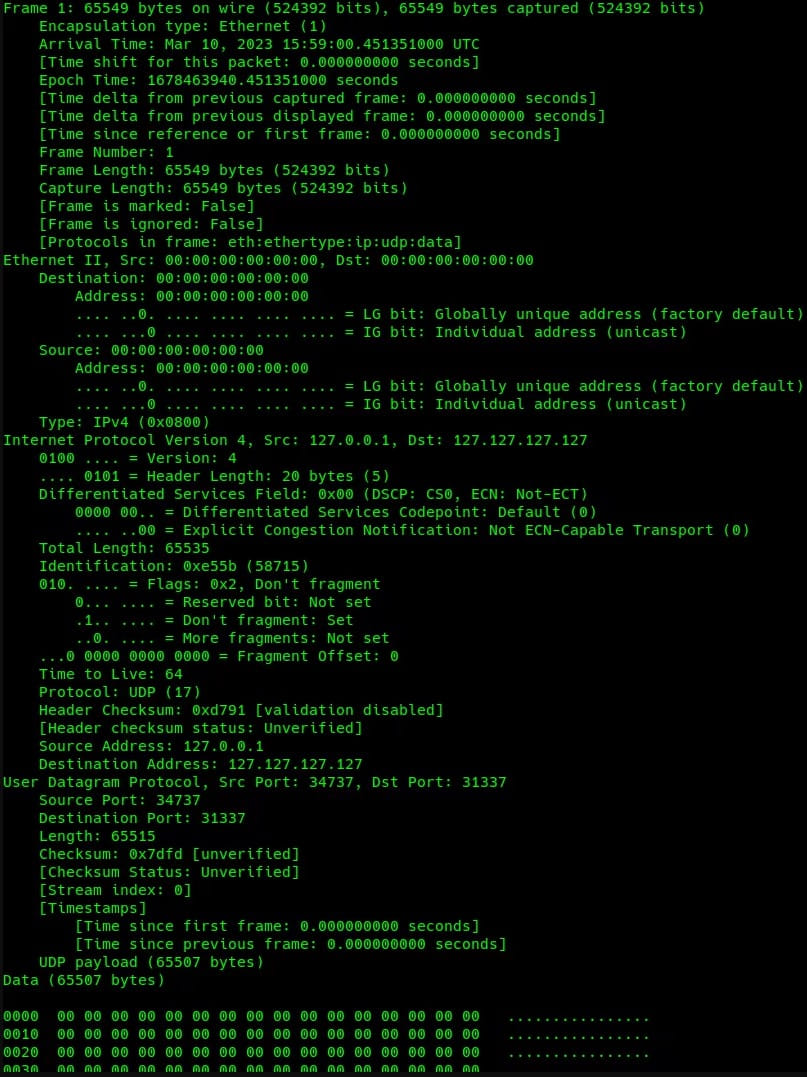
HTTP floods generate huge volumes of site requests, whilst UDP flood sends huge volumes of rubbish site visitors to the objective; therefore the 2 strategies try to succeed in an outage the usage of a distinct manner.
Akamai benchmarked the botnet in 10-second assaults for each HTTP and UDP, and within the HTTP assault, the malware generated 20,430 requests for a complete measurement of three.4 MB. The UDP flood generated 6,733 applications totaling 421 MB of knowledge.
The researchers estimated that with 1,000 nodes, the UDP flood may generate more or less 336 Gbps, whilst at 10,000 nodes, the assault information quantity would achieve 3.3 Tbps.
Relating to the HTTP flood, 1,000 ensnared units would generate 2,000,000 requests according to moment, whilst 10,000 nodes would take that choice of 20,400,000 rps and 27 Gbps.
HinataBot remains to be in construction and may put into effect extra exploits and widen its focused on scope anytime. Moreover, the truth that its construction is so lively will increase the possibility of seeing stronger variations circulating within the wild quickly.
“Those theorized functions clearly do not take note the other forms of servers that will be collaborating, their respective bandwidth and {hardware} functions, and so on., however you get the image,” warns Akamai.
“Let’s hope that the HinataBot authors transfer onto new leisure pursuits ahead of we need to take care of their botnet at any actual scale.”